Like so many aspects of this fizzled scandal, there is less to this story than meets the eye.
Yes, the Justice Department on March 16 moved to drop the case against Concord Management and Consulting, which was indicted two years ago for spreading disinformation on social media during and after the 2016 election. And two of the prosecutors who signed the motion to drop the case worked for former Special Counsel Robert Mueller. The decision was not the result of political interference or pressure, but rather a recognition that the indicted parties were using the trial process to learn how the U.S. government caught them in the first place.
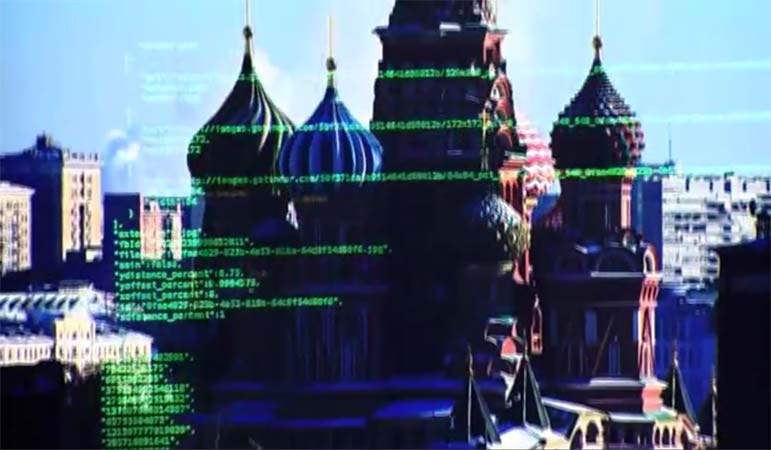
As the Justice Department's motion to dismiss the Concord defendants says: "A trial of this case risks publicizing sensitive law enforcement information regarding measures used to investigate and protect against foreign influence over the political system." In some ways it already has. In late 2018, a new Twitter account posted what it claimed to be a Justice Department database that included information obtained by a U.S. hack of Russian servers involved in the 2016 disinformation campaign. The account publicized information the defendants were provided during the discovery process before trial.
Of the many implications of the government's dismissal of this case, the most important is this: It reveals the limits of a strategy to fight foreign adversaries through indictments and prosecutions. The U.S. government has many tools to deter cyberpowers from attacking U.S. citizens and corporations. It can launch its own cyber counterattacks. It can sanction entities in foreign governments that engage in this hacking. It can use diplomacy to try to persuade or pressure adversaries to back off.
More recently, the U.S. government has also started indicting the foreign hackers themselves. In 2014 the Justice Department indicted five Chinese military hackers for economic espionage, hacking U.S. businesses to steal trade secrets. "State actors engaged in cyber espionage for economic advantage are not immune from the law just because they hack under the shadow of their country's flag," said the prosecutor at the time.
Like Mueller's indictment of Russian hackers and front companies, the 2014 prosecution showed that the U.S. government was able to piece together an elaborate scheme orchestrated by Chinese hackers to conceal their identities and the location of the computers used to commit these crimes.
The 2014 indictment and others that followed were not intended to bring the defendants to trial. Indeed, part of the calculation for publicizing such indictments was an assessment that the defendants would never show up in court. If the Justice Department believes there is a chance a defendant will travel to a jurisdiction where he could be arrested, then the indictments would remain under seal, said John Demers, assistant attorney general for national security.
When that outcome is unlikely, "the value of unsealing the indictment and telling people who stole the data outweighs the slim chance we might be able to catch them," he told a security conference last month.
In this respect, unsealing the indictments served two purposes. It deterred foreign powers by demonstrating America's capabilities to identify foreign hackers. And it reassured the victims of foreign hacks and the wider public that the U.S. government was taking these crimes seriously.
This time around Concord called the prosecutor's bluff. Lawyers representing the companies participated in the legal process, even though the Justice Department said it never believed the company would accept a ruling from a U.S. court. The defendants were "availing themselves of the discovery process while still perhaps evading justice if the case moves forward," says Columbia University law professor Matthew Waxman.
This does not mean public indictments of foreign hackers are always wrong. But it does show the risks of using the U.S. system of justice as a tool of foreign policy. American due process is designed to protect the rights of the accused. It was not designed to protect the sources and methods the U.S. government uses to catch spies and hackers.
Sign up for the daily JWR update. It's free. Just click here.
(COMMENT, BELOW)
Eli Lake is a Bloomberg View columnist who writes about politics and foreign affairs. He was previously the senior national security correspondent for the Daily Beast. Lake also covered national security and intelligence for the Washington Times, the New York Sun and UPI, and was a contributing editor at the New Republic.


 Contact The Editor
Contact The Editor
 Articles By This Author
Articles By This Author